5 Common Myths About Privileged Access Management Infographic
[...]
Try CyberFOX Platforms for Free. 14-Day Free Trial

This comprehensive guide delves into the principle of least privilege, a key security concept that restricts user access rights to the bare minimum necessary to perform their roles. Through practical insights and real-world examples, this eBook explains how MSPs can implement least privilege policies effectively, mitigate risks, and protect client [...]

As cyber threats become more complex, the cost of preventing them is simultaneously rising, but the good news is that improving your security stack doesn’t have to exhaust your IT budget. Even the most secure systems are not 100% immune from attacks, and when those attacks result in a successful [...]

The deadline for complying with the updated FTC Safeguards Rule was June 9, 2023. Are you in compliance? The Safeguards Rule requires any business entity that is categorized as a financial institution to comply with security principles designed to protect non-public personal information. Some companies that were not considered financial [...]

Two-factor authentication (2FA) has been a standard security measure for over a decade. Whether logging into an online bank account, accessing work email, or managing sensitive client information, most internet users have encountered 2FA in some capacity. That’s because the data shows that it works. According to a 2019 study [...]

Building an efficient IT department and strong tech culture is a team effort that requires the cooperation of every employee. From your newest hire to your CEO, all team members need to know what constitutes good cyber hygiene, understand how they contribute to cybersecurity, and commit to following stated policies [...]

Cybersecurity measures have improved dramatically over the past decade. As technology platforms and applications have become more sophisticated and complex, so have the security systems and tools that protect them. As new 2nd generation anti-virus software, advanced UTM firewalls, threat detection and response systems, and other protocols are more widely [...]

For many IT administrators and end-point users, administrative privilege has become a source of friction. Security best practices recommend protecting your privileged accounts by limiting administrative privilege to reduce your attack surface, activating user account control (UAC), and implementing strong password policies and controls. However, these practices aren’t always easy [...]
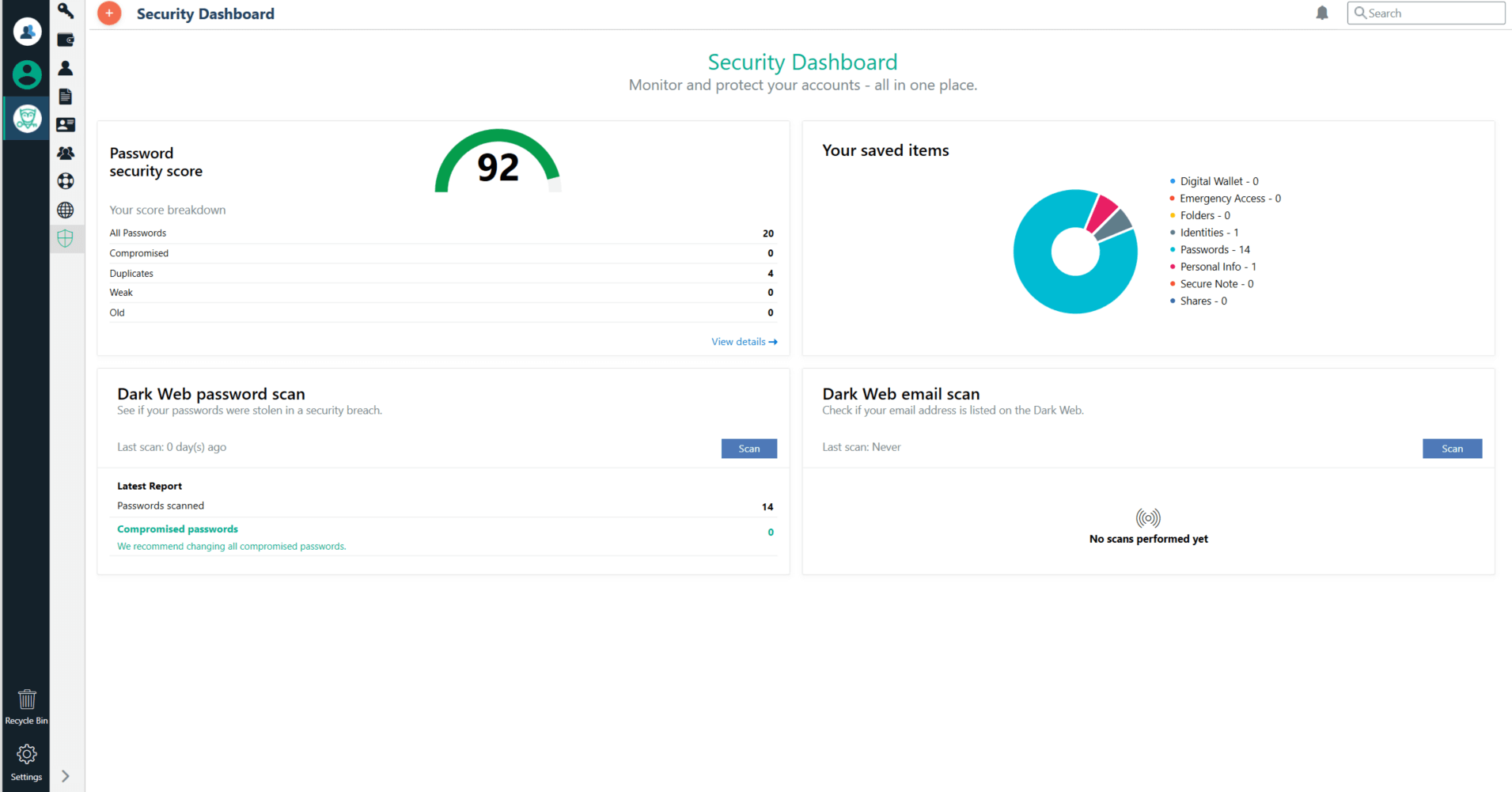
One of the most important things you can do to reduce risk across your organization is to crack down on password security. According to the Ponemon Institute’s 2020 State of Password and Authentication Security Behaviors Report, 50% of IT professionals reuse passwords across workplace accounts, and 49% sometimes or frequently [...]